The call came from a number I didn’t recognize, with a Canadian area code.
A steely voice on the other end of the line greeted me, identifying himself as an official with the Canadian military.
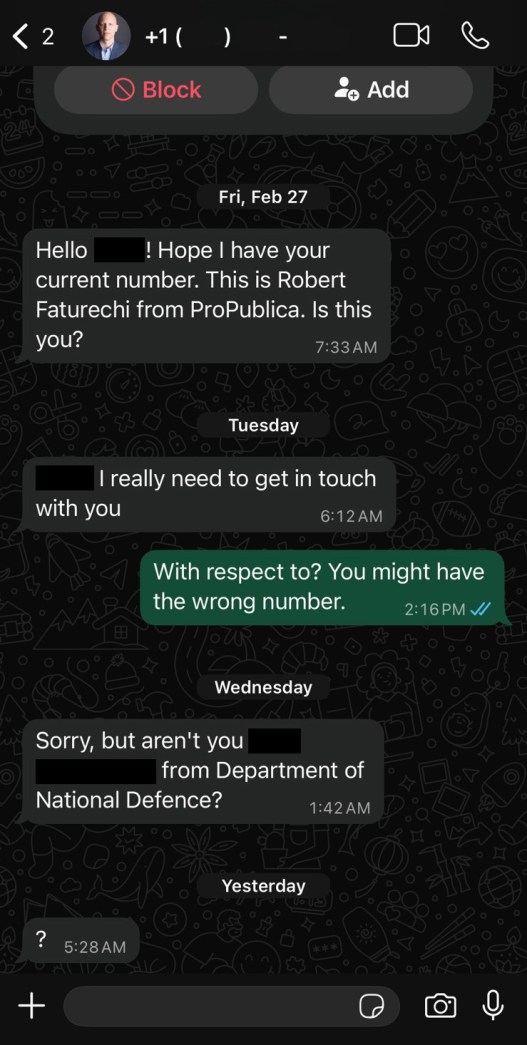
He had a question: Had I been reaching out to him on WhatsApp, trying to work him for information?
I paused. As an investigative reporter at ProPublica, I’m reaching out to a lot of people all the time. But as I racked my brain, I couldn’t think of any Canadians I had recently tried to develop as sources.
It seems as though someone is impersonating you, the man warned.
I was at a loss. What was Fake Me asking about? Were they just using my name or my picture too? How could I be sure the person warning me about this impostor wasn’t actually an impostor himself?
The Canadian official assured me he’d send a message from his government email to confirm his identity, and he’d include screenshots of his conversation with Fake Me. I thanked him, and we exchanged some pleasantries. Before saying goodbye, I asked him if there was anything he’d like to get on the radar of an investigative reporter. (Without even realizing it, I was working him for information. Maybe Fake Me and Real Me aren’t so different.)
The screenshots the Canadian sent over later showed someone with a Miami number using my ProPublica headshot as their profile pic. I’ve never lived in Florida.
“This is Robert Faturechi from ProPublica,” Fake Me wrote. “I really need to get in touch with you.”
The Canadian asked me not to publicly reveal too many details about his work, but it involves dealing with other countries, including Ukraine.
I alerted our security team at ProPublica. They told me that there was little we could do aside from reporting the fake account to WhatsApp.
We did, and I put the matter behind me — until two weeks later, when I got another warning.
This time it was a Latvian businessman who said he runs an organization providing equipment to the Ukrainian military and is involved in a drone development project with Ukrainian forces.
“Hey!” the Latvian wrote to me on LinkedIn. “Was good to chat on Signal! Let’s connect here as well!”
The only problem was I had never chatted with him on Signal, the encrypted messaging app.
The Latvian reached out to me on LinkedIn because he was concerned he wasn’t talking to Real Me on Signal. He sent over screenshots of someone using my headshot and claiming to be me.
“Am I right in understanding that you are an expert in the field of UAVs?” Fake Me had messaged the Latvian, referring to unmanned aerial vehicles, a fancy term for drones.
“My clients,” the impostor explained, “are particularly interested in the application of UAVs in Ukraine.”
The Latvian had offered to discuss the topic in a phone call, but Fake Me (who could be a man or woman) declined, saying they weren’t “comfortable” talking on the phone. They asked to continue the “conversation in written format” or if the Latvian could “record a voice message on this topic.”
The Latvian, growing suspicious, insisted on a video call. Fake Me relented, sending him step-by-step instructions they said would result in a secure video chat, but that actually appeared to have been an attempt to trick the Latvian into giving up access to his email account.
The Latvian ultimately blocked Fake Me.
The impersonations were disquieting. Investigative reporting is hard enough with public trust in media so low and those in power stepping up attacks against journalists. Scammers giving potential sources another thing to worry about just makes our work more difficult.
I can’t be certain what Fake Me is up to, but posing as a journalist in this way seems to be the latest evolution in online deception. ProPublica has chronicled the dark world of pig butchering, in which human traffickers in Asia force their victims to scam people by posing as friends or potential romantic interests. In those cases, the goal is cash.
But sometimes the objective is stealing sensitive information. And even sophisticated actors can fall victim to so-called phishing attacks, in which scammers impersonate legitimate entities. One of the most notable and perhaps consequential instances was when John Podesta, chair of Hillary Clinton’s 2016 presidential campaign, fell victim to an email purporting to be a Google security alert, giving hackers access to his personal Gmail account. Thousands of his emails, some of them quite damaging to Clinton and the Democratic Party, were published online.
From the screenshots the Canadian and Latvian sent me, I could tell Fake Me wasn’t asking for credit card info or urging anyone to buy a gift card. It didn’t appear to be a moneymaking scam.
I’m not sure who else they’ve reached out to, but in both cases I was alerted to, Fake Me seemed to have an interest in foreign militaries. Maybe some clunky intelligence operation?
I tried calling Fake Me using the phone number they used to reach out to the Canadian defense official. I got a recorded message saying the line was not in service.
On Signal and WhatsApp, the number rang and rang, without an answer.
There was even less we could do about the second impersonation than we could about the first.
Signal keeps extremely little information about its users; it knows when someone first created their account and the phone number they used to do so but stores nothing about who they’re messaging. That’s by design. The hands-off approach is part of why it’s a safe platform for journalists to talk securely to sources. But it also makes catching impostor accounts difficult. Red flags, like sending messages with suspicious links, aren’t detectable by Signal. (WhatsApp can’t see the content of messages unless a user reports them. It has the ability to see who its users are messaging, but a spokesperson said it’s rare for the company to store that data.)
Cooper Quintin, a technologist at the digital privacy nonprofit Electronic Frontier Foundation, said he had never heard of a case like mine on Signal. But overall he was noticing an upswing in scams on the secure messaging app. Signal was doing what it could, he said, such as adding a feature that slows down would-be spammers trying to send many messages in a short time frame. Signal also makes links from unknown senders unclickable. But there are limits to what Signal can do, he said, without compromising its hallmark privacy protections for its users.
“This fits a trajectory. As Signal gets more popular, more attackers start to view it as a potential platform for attacks,” said Quintin, who insisted we talk via video chat so he could be sure I wasn’t an online impersonator asking to interview him about being impersonated online.
Some platforms — such as Facebook and Instagram — allow users to get verified accounts in which the site essentially confirms they are who they claim to be. But it wouldn’t be feasible for Signal to do the same, said digital security expert Runa Sandvik, who consults on security matters for ProPublica. The nonprofit that runs Signal is small, and verification would require staffing it doesn’t have. More significantly, she said, it would require Signal to collect more information about its users, eroding the privacy protections that make it popular.
Signal did not provide comment for this article. A spokesperson for WhatsApp said “we have a strong track record of banning those trying to scam others and staying ahead of scammers and their tactics.” The spokesperson said WhatsApp “took appropriate action in line with our policies” against the account spoofing me but declined to say what that action was. In general, WhatsApp tries to root out scam accounts, even before they’re reported, by monitoring for suspicious behavior that includes attempting to launch many accounts from a single location.
It turns out, if you’re contacted by someone pretending to be a reporter, the best way to scuttle their scam is to do a little reporting of your own.
Every journalist at ProPublica has a bio page. Here is mine. On my bio page, you’ll find my Signal handle and email if you click on the Contact Me button. You can always check the Signal information or email address on my bio page to verify that I’m the person contacting you.
This is true for every ProPublica reporter: We all have our Signal numbers or usernames on our profiles, and we all have an email ending in @propublica.org.
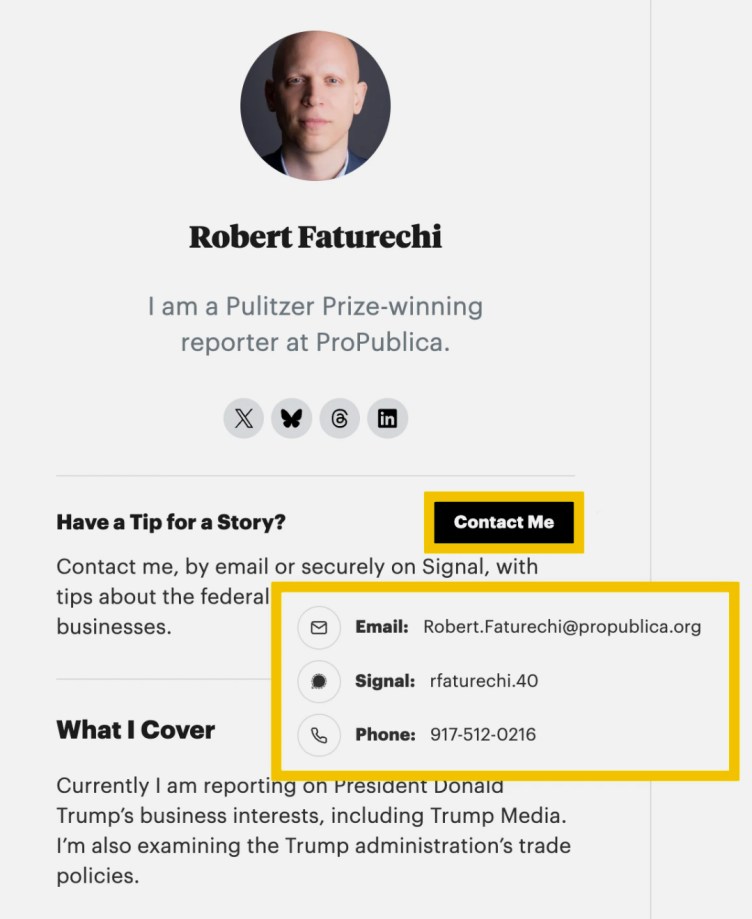
The same goes for reporters at other outlets. If one reaches out to you and you have doubts, check their website and social accounts to verify their email or Signal or WhatsApp numbers. We’ve heard through the media grapevine and in published accounts about scams similar to mine hitting other organizations as well.
They include smaller-scale deceptions. The New York Times recently flagged an account on X falsely claiming to be an intern for the news organization. In 2023, Reuters reported that two of its reporters in China were being impersonated via Instagram and Telegram accounts that were attempting to get information on activists protesting the country’s COVID-19 policies. And just this month, a correspondent for Reuters in Saudi Arabia warned his followers that someone was impersonating him on WhatsApp.
There are also more sophisticated campaigns to be on alert for. The German government this year released a vague warning about what it described as likely a state-sponsored actor attempting to commandeer the Signal accounts of government officials and reporters across Europe. And last month, the FBI announced that individuals associated with Russian intelligence were posing as Signal’s security department to fool American government officials and journalists into providing information that would allow the hackers to take over their accounts. Once they had access, the FBI warned, they could see conversations and contact lists, and send messages as the victim.
These scams should worry anyone who cares about investigative reporting. Throughout my career, I’ve done sensitive stories exposing wrongs in politics, finance, the military and law enforcement. Many of them relied on courageous individuals who have taken leaps of faith and shared information, sometimes at real personal risk. I go to great lengths to protect my sources and make sure they are comfortable taking that risk. If potential sources have to doubt that I am who I say I am, they may be less likely to engage.
When journalists are impersonated online, like I have been, Sandvik said they shouldn’t be quiet about it.
“If and when it does happen, be very public about it, which is what you’re doing now,” she said. “Let people know this is happening so if people hear from you, they know this is something to look out for.”